By Cheryl Leisk

In these days of heightened security to know your doors are actually locked is a critical issue in meeting the many challenges facing crime prevention and counter-terrorism initiatives. There is now a new product on the market called the security Microswitch Box which is a hardware device that integrates and enhances existing security monitoring systems by monitoring lock status and works in conjunction with existing security software.
Initially, you may not put a great deal of emphasis on the importance of this but when it comes to a cost-effective solution to integrate locking hardware with existing security technology this product is leading-edge innovation at its best. It’s not high-tech, complex or expensive equipment but has the potential to save organizations thousands of pounds in preventative security management.
A range of microswitch boxes have been designed and developed by Trevor Leisk, Director of AMS Australia Pty Ltd., following over 20 years of experience working in the security industry on high security applications. The idea of the microswitch box was developed out of sheer frustration as there was no existing hardware on the market that could reliably monitor lock status at all times, an imperative for top secret secure applications. This included the ability to ensure that an EOLM (End Of Line Module) could also be housed offering tamperproof capabilities if required.
And so when push came to shove, the motivating force behind this innovation stems from a comment made by a project contractor who said, “If you don’t like the way we’re doing this, then you come up with something better.” And that’s exactly what happened!
To put this into context, let’s apply an everyday occurrence that, on the surface, is one of human habits rather than someone deliberately setting out to breach security. Nonetheless, it can have serious security implications in terms of understating security risk.
A COMMON SECURITY BREACH
Take a common everyday scenario. In recent years, smoking in some buildings is now prohibited leaving smokers to exit the building and smoke outside. In some cases smokers exit through a fire door which is designed to be used as an emergency escape exit only. It is well known that the operation of the fire exit lock operates from the inside and under normal circumstances a fire exit door is not to be used randomly or otherwise as an entry point. So, let’s say, for example, that an individual jams the fire door bolt back to stop the door latching so they can exit and re-enter the building throughout the day between breaks. A typical security breach has now occurred and the building has been rendered insecure. Of course, this is an unintentional security breach which can equally be played out as an intentional security breach.
What happens now? The central alarm station has monitored that the fire door is closed assuming that the building is secure. The reed switch has done its job in registering that the door is in fact closed. Everyone leaves work on Friday night and the last person to re-enter through the fire exit door forgets to remove the obstruction from the lock. Physical security checks of perimeter doors may not take place for some hours, effectively leaving the building exposed. A major security breach is now unfolding.
How would the application of the microswitch box overcome this problem?
The installation of the microswitch box would allow not only the central monitoring station to indicate that the door is closed but that the door lock has actually engaged.
In this scenario it would ensure that perimeter security is maintained in the absence or delay of physical security checks. Alternatively, the microswitch box can also be used to monitor if security patrols have physically checked all perimeter access points by providing an audit trail. This then provides evidence that physical security monitoring has been undertaken and is a ‘win win’ for both organizations and physical security personnel in minimizing human error.
Additionally, security personnel can effectively monitor lock status in situations where remote outstations are not subjected to regular physical security checks ensuring the integrity of the security is maintained. There are also those added situations where, due to high levels of personal risk associated with some occupations monitoring of lock status is achieved at a central alarm station. This is particularly relevant in custodial situations.
HOW DOES THE MICROSWITCH BOX WORK?
For years now, magnetic or balanced reed switches have been used to monitor door status. Now the innovation of the microswitch box adds a further degree of security with the built-in capability of also monitoring the status of the door lock. This is achieved through utilizing a tamperproof microswitch box that not only incorporates a reed switch but also monitors the lock status. When the engaged lock depresses a plunger it then activates the microswitch in the box which sends a signal to a central monitoring station to say that the lock is engaged. This then provides dual discreet monitoring which is not detectable or ‘hidden in full view’.
The microswitch box is designed to replace an existing lock striker plate and can be retrofitted into a door frame or an access point. It can then be wired into existing security management systems and can incorporate an EOLM in a tamper evident environment. This means that any unauthorized activity to gain access to the EOLM or to disable the unit were to occur an alarm would be activated.
For those areas that do not require top secret secure applications the microswitch box can simply accommodate a standard alarm system. In this case, the microswitch box could be used in a stand-alone configuration. In addition, there is an optional door hold-open sounder which can be fitted into the microswitch box which will give an audible sound that can alert those in the vicinity that the door is not secure and that the lock has not engaged.
An important feature of the microswitch box is its ability to integrate security software technology with existing mechanical lock hardware. This means that there is no need to replace existing systems or hardware but that this can simply enhance what is already present in a cost-effective way.
COMPATIBILITY
The large range of microswitch box products means that there is a compatible model for most good quality locks and a range of finishes to match existing door furniture. So whether it is a new installation or a heritage listed building there is no need to alter existing locks or door furniture in order to enhance existing security. The microswitch technology can also be designed around particular and unusual applications. A brief overview of the diversity of applications is discussed further but by no means limited to those mentioned here.
|
|
|
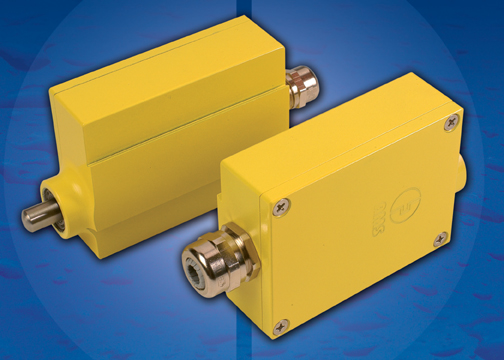
MF Box (Photo by AMS Australia Pty Ltd.) |
APPLICATIONS
Critical Infrastructure Protection
The microswitch box has been used extensively in top secret secure applications and has particular relevance in providing additional security for critical infrastructure such as telecommunication pits, energy utilities including gas and water, airport security and diverse applications such as road manhole covers. In fact, any access point that may be vulnerable to potential terrorism or unauthorized activity of any kind. CCTV surveillance, in conjunction with lock hardware monitoring, would have the ability to pin-point a security breach aiding security risk assessment strategies and crime prevention.
The Multi-Function Microswitch Box (MFMB) has been designed specifically for these applications and has the ability to house an EOLM, has a weather-resistant exterior made from solid aluminium and offers a variety of stainless steel plunger lengths and spring tensions, depending on applications.
CCTV Activation
Using the standard microswitch box for door lock applications can activate CCTV equipment where continuous surveillance may or may not always be necessary. It is simply a case of wiring the CCTV equipment to the microswitch box located inside the door hidden from view. The camera surveillance will immediately activate once the door lock is opened which then alerts the central monitoring station that access has occurred. This is particularly useful when monitoring only needs to occur at times of activity through access points.
Educational Environments
Additional security requirements in our schools and institutions says a lot about the world we now live in creating a greater awareness of the need to approach security management in a more comprehensive way. For example, in situations where classrooms are in ‘lock-down mode’ the installation of a microswitch box attached to an LED light indicator, located by the door, would allow staff to visually confirm that classroom doors are locked. Alternatively, this could also be achieved from a central monitoring system.
In this example, it means that those inside the classroom could still ‘free-handle’ out if necessary while a potential intruder could not gain access to the classroom from the corridor. The aim of this exercise is to ensure that the locks have actually engaged, thereby ensuring the safety of those inside.
While this only provides a sample of applications, there are of course many more examples including custodial, hospitals, nursing homes and freezer doors (protecting scientific research) to mention just a few. What this means is that we need to look very closely at all those areas that we have so often taken for granted and critically assess the need to integrate security more effectively.
However, one thing is certain; crime is something that will not go away. As the British Chamber of Commerce (BCC) reported, crime creates a barrier to economic growth with estimations that crime costs businesses in excess of £5,000 per year. The important point is to remember that preemptive measures and better security practices can make inroads into crime prevention. Not all security solutions need to be exorbitantly expensive to be effective. It could be as simple as making sure that you’ve ‘locked the door on your way out.’
Cheryl Leisk is Director of AMS Australia Pty Ltd.
(www.amsaustralia.au.com).
For more information, please send your e-mails to swm@infothe.com.
ⓒ2007 www.SecurityWorldMag.com. All rights reserved.
|